If you think that Hashing, Encryption, and Encoding are the same then you are completely off the mark! however, you are not alone. They sound very much similar but actually, they are not.
Before understanding Hashing, Encryption, and Encoding, let’s understand a few things first regarding Internet security. From the security point of view, what are the most important things, when sending data or messages on the internet?
- You want to let other people know that the message is sent by you, not by anyone else
- In addition, you want the message should be in the same format without any modification.
- Even you want to protect your message from ill-intended people.
The above three functions can be summaries in 3 steps :
- Identity Verification
- Integrity
- Confidentiality
Hashing
Let’s try to imagine life without hashing. Suppose It’s Alpha’s birthday and you decided to send a “Happy Birthday” message.
But your geeky friends decided to have a bit of fun at your expense. So they intercept the message and turn your “Happy Birthday” message into a ” Rest In Peace” message. (Imagine the consequences). This could happen and you wouldn’t even know it.
Hashing protects the integrity of your data, against potential alteration so that your data isn’t altered one bit.
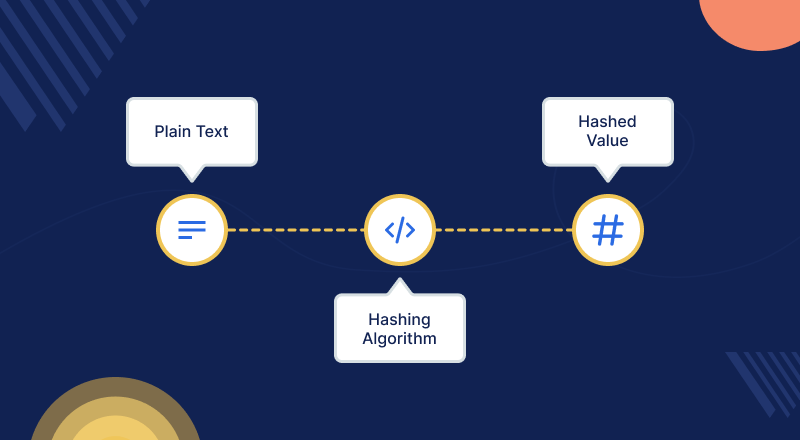
Hash is a value that is formulated from the text, number, or anything through a hash algorithm, this number is of fixed length irrespective of the original text length. These algorithms are formulated so that no two hashes should be the same. And it is impossible to go back from the hash value to the original text.
Now let’s say, you have sent a file with its hash value, and in between the file has been compromised. Therefore, when the receiver calculates the hash of this compromised file, he will receive a different hash value.
Then at this point, they “‘ll know the message is been altered. Hashing is unique. Even the tiniest bit of change will alter the hash value completely i.e. Avalanche Effect.
Hashing algorithm
Use of Hashing
- It is an effective method to avoid data duplication in the database.
- In addition, hashing is used in digital signatures and SSL Certificates.
- We can find a specific piece of data in a big database by using hashing.
- Computer graphics also use hashing widely.
Encryption
- It’s almost impossible to imagine the internet without Encryption. Encryption is what keeps the artificial world of the internet secured. Encryption keeps data secured and confidential.
- Fundamentally, it is the process of transforming your confidential data into an unreadable format so that no hacker or attacker can manipulate or steal it. Thereby, serving the purpose of confidentiality.
- With the help of cryptographic keys, we can achieve encryption. The information is encrypted before it’s sent and decrypted by the receiver. Therefore, the data is safe when it is “in the air.”
- Based on the nature of the keys, encryption can be classified into two main categories – symmetric encryption, and asymmetric encryption.
- The Public Key is virtually everywhere. Even you possess it without even knowing it. One is stored in your web browser every time you visit an HTTPS-enabled website. When you send any data to an encrypted site, it is encrypted using the Public Key.
- The Private Key, on the other hand, is only with the receiver. Private Key will come into function to decrypt the data. The use of two different keys makes the encryption process more secure and a tad slower.
- The Asymmetric Encryption is first applied for the SSL handshake process — server validation if you call it. Once the connection is in place between the server and the client, Symmetric Encryption takes care of the data encryption.
To know more about the cryptographic methods, please refer to the Blog.
Encoding
- Unlike Encryption and Hashing, Encoding is not suitable for security purposes.
- Fundamentally, it is just a technique to transform data into other formats.
- So that numerous systems can use it.
- There is no use of keys in encoding.
- The algorithm that is used to encode the data is used to decode it as well.
- ASCII and UNICODE are examples of such algorithms.
So we have discussed, Hashing A string of numbers generated to confirm the integrity of data through hashing algorithms.
Encryption A technique used to maintain the confidentiality of data by converting the data into an undecipherable format. Encoding A conversion of data from one format to another format and in our next blog, we’ll discuss it in more depth.
Besides that, if you are looking for a security audit service, that identifies vulnerabilities like cross-site scripting, guessable credentials, unattended application security flaws, and other misconfigurations in your e-commerce store, check out the Webkul basic security module.
Check out this Magento-based e-commerce store security extension which can be customized.
Need Support?
Thank you for reading the blog!
For further more interesting blogs, keep in touch with us. If you need any kind of support, simply raise a ticket at https://webkul.uvdesk.com/en/.
You may also visit our Odoo development services and quality Odoo Extension.
For further help and queries, please contact us or raise a ticket.


Be the first to comment.