With an increasing number of users on the internet and increasing online transactions, personal information is flowing throughout the world at a speed that could not have been imagined before.
However, such benefits come with challenges. With the advent of the internet, computer crimes have increased. Identity theft is one of them.
What is Identity theft?
The concept of identity theft comes into the picture when someone unauthorizedly collects another person’s personal information and uses it for criminal reasons such as mail redirect, opening a bank account, etc.
It is a criminal activity in which criminals steal sensitive data from people using Social Engineering, Email Spamming, and Dumpster Diving, and then use this information for personal benefits, fraud, revenge, and other illegal activities.
Identity theft is one of the leading problems in the world and cyberspace.
It evolved over the last 25 years. According to the U.S. Federal Trade Commission, approx 9 million Americans have stolen their identity each year and in India, identity theft has become the fastest-growing crime.
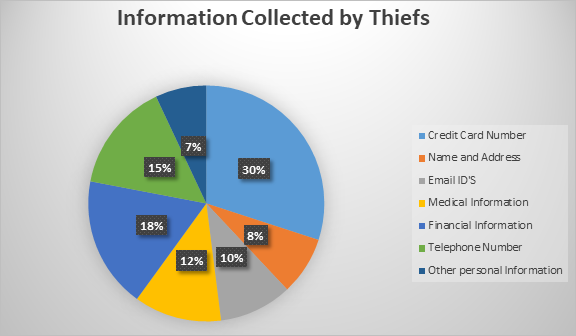
Type of information collected by fraudsters
Fraudsters steal the personal and financial information of a person to obtain goods and services.
They steal identities such as Name, Gender, Email IDs, Medical information, Credit card number, Passport Information, Driving License, Family Information, Date of Birth, Age, Marital Status, Religion, Telephone no. and much more.
The figure shows the most common type of information collected by thieves.
Once fraudsters have your personal information, they can get medical treatment on your health insurance, create a social media account, and can open a bank account.
Many fraudsters sell this information on the dark web or can use it for other criminal activities so that they can hide their identity and no one can trace them.
Methods used by identity thieves
- Social Engineering (Phishing, Vishing, Smishing)
- Dumpster Diving
- Hacking (SQL Injection, MITM, Zero-Day Attacks)
- Skimming
Safeguards
- Check your bank and credit card statements frequently.
- Do not provide information over the phone to unknown malicious actors.
- Don’t click on an email or pop-up link asking for personal or financial information.
- Always use long and strong passwords.
- Avoid using the same password for multiple websites.
- Turn on the phishing detector on your computer/browser.
- Never display financial or personal information on social media.
Conclusion
Identity theft can be costly, both financially and emotionally.
However, by understanding the ways of criminals and taking measures to stop people from getting hold of your personal information, we can reduce the risks of being the victim of identity theft.
It is difficult for authorities to detect attackers who are committing these frauds because they are daily inventing new ways to penetrate.
The implementation of stronger security measures on devices through which information is being transferred is a must. Always give priority to information and keep it safe from bad actors.
Besides that, looking for a security audit service? That identifies vulnerabilities like cross-site scripting, guessable credentials, unattended application security flaws, and other misconfiguration in your e-commerce store, check out the Webkul basic security module.
Check out this Magento 2-based eCommerce store security extension which can also be customized.
Need Support?
Thank You for reading this Blog!
For further more interesting blogs, keep in touch with us. If you need any kind of support, simply raise a ticket at https://webkul.uvdesk.com/en/.
You may also visit our Odoo development services and quality Odoo Extensions.
For further help or queries, please contact us or raise a ticket.